Baking a crime (a recipe of disgust in three easy steps)


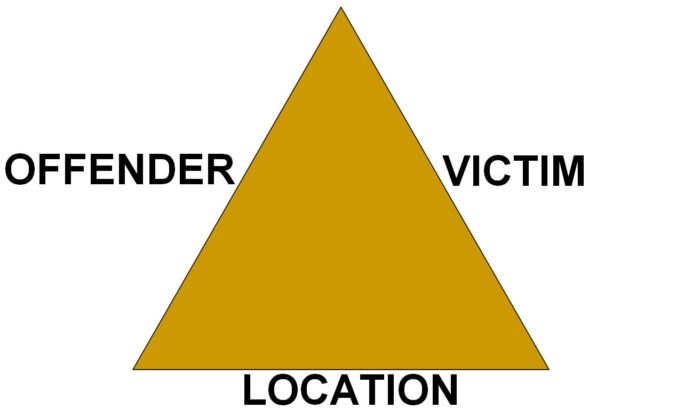
This baking challenge aims to bake the perfect crime-cake.
Please don’t be put off by the appearance of this crime-cake; I’ll admit it looks a bit unconventional, as it comes in the shape of a triangle.
Patrol member demonstrates a snare, South Luangwa National Park, Zambia © Mary Rice/EIA
But never mind, that doesn’t mean it’s less tempting than a regular cake (in fact, to those who eat it, it’s supposed to taste very good).
Now for the good news, which is always welcome at the beginning of a recipe: this cake has only three ingredients. Three ingredients make the three sides of our crime-triangle-cake.
Hands washed? Apron on? Right, then. Take a bowl and begin by measuring out your location. This forms the base of the cake. After all, it’s important that the crime happens somewhere.
The practiced baker will bear in mind how the location will complement the two ingredients to follow, such as whether the location is accessible or whether its guardians are under-resourced – then the more accommodating this location base will be to the overall crime-cake.
That’s one side of the triangle done already! Now to the second – we need someone to put the ‘crime’ into this crime-cake. Yes, we need an offender.

Members of South Luangwa Conservation Society © Mary Rice/EIA
Forest Department Officer in India gathering evidence © EIA
But which offender to choose? If years of baking have resulted in kitchen
cupboards crammed with slightly different versions of the same ingredient, choose the one you know will work best. A trusty one, a well established one. One that’s had the time and opportunity to build up all the necessary contacts, knowledge and expertise.
The offender with longevity is best, not least because the fact he’s still around suggests the absence of risk. You might notice that this offender has been operating for a significant amount of time in one place but remains mysteriously unruffled by the law … well, it doesn’t mean nobody knows what he’s up to, it’s just that political connections and corruption give him a helping hand.
Now, hang on a minute. Should you experience the unfortunate event of opening the cupboard to find the offender strangely absent, please DON’T PANIC. Take comfort from recent events. One such convict and hundreds of his ilk had been in prison, but don’t worry – they’ve just been given a Presidential pardon! Bonus time! We’re back in business!
So pluck your offender from the shelf, ensure he’s well-equipped and well paid-off, drop him into the location and stir well.

The victims: Samburu National Park, Kenya © Mary Rice/EIA
Onto for the final part. What else does this crime cake need? Hmm … oh yes, of course. A victim.
To complete a successful crime-cake, you’ll need a victim that is in demand, easy to move to market and one that fetches a high price.
Now take note. It’s also very handy if the people who decide on priorities are constrained or unaware or, best of all, just not bothered about this particular victim.
This final stage adds real depth of flavour to the cake. Choices, choices: bear, tiger, leopard, snow leopard, clouded leopard, cheetah, lion, deer, civet, binturong, rhino, elephant, pangolin, shark, snake, tortoise, turtle, lizard, sea cucumber, giant clam, then primates, birds and frogs… I almost forgot to mention, these ingredients can be live or dead and dismembered. And let’s not overlook plants and timber.
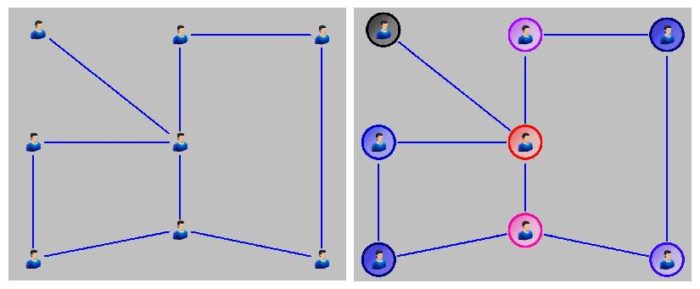
Mapping the associations in a criminal network, then identifying and targeting the key individuals, will focus investigations. The second example here, right, is called social network analysis
Phew, just looking at the list is exhausting (speaking of which, this bounty is a bit deceptive – you’ll find that the more often you make this cake, there will be fewer and fewer of these ingredients left).
And so, quite quickly, we reach the end of our recipe. Your triangle-shaped crime-cake is now ready for the oven. Bake at 180°c until golden with high profit, firm with low risk, and the knife comes out clean.